GET logs-sentinel_one.agent-kdb/_search
ES|QL Query
기본 문
FROM logs-*
| WHERE event.code IS NOT NULL
| STATS event_code_count = COUNT(event.code) BY event.code,host.name
| ENRICH win_events ON event.code WITH event_description
| WHERE event_description IS NOT NULL and host.name IS NOT NULL
| RENAME event_description AS event.description
| SORT event_code_count DESC
| KEEP event_code_count,event.code,host.name,event.descriptionFROM 에서 처리하고자 하는 데이터를 제공합니다. 처리는 위에서 아래로 순차적으로 실해되며, 한 블럭의 결과는 다음 블록의 입력으로 전달됩니다.
EVAL 은 레코드별로 새 필드를 생성합니다.
임의의 인사정보를 생성하여 인덱스로 만듭니다.
b2656b6407614109ae75222e22eec16e, 172.16.4.135, 00-0C-29-40-09-C1, user1, Marketing
7aa4d173098e471081ef30104c23448f, 172.16.4.90, 00-0C-29-13-D8-A0, user2, Sales
193b90cbde4b4084b4d3c1abdbad3f95, 172.16.4.128, 00-0C-29-0E-F9-D6, user3, Account
72e6408d1fb840a89dd9596aa03b4825, 172.16.4.128, 00-0C-29-0E-F9-D6, user4, Sales
POST /_bulk
{ "create" : { "_index": "employee0209" } }
{ "sentinel_one.agent.uuid": "72e6408d1fb840a89dd9596aa03b4825", "ip": "172.16.4.128", "mac": "00-0C-29-0E-F9-D6", "username": "user4", "dept": "Marketing"}
{ "create" : { "_index": "employee0209" } }
{ "sentinel_one.agent.uuid": "7aa4d173098e471081ef30104c23448f", "ip": "172.16.4.90", "mac": "00-0C-29-13-D8-A0", "username": "user2", "dept": "Sales"}
{ "create" : { "_index": "employee0209" } }
{ "sentinel_one.agent.uuid": "193b90cbde4b4084b4d3c1abdbad3f95", "ip": "172.16.4.128", "mac": "00-0C-29-0E-F9-D6", "username": "user3", "dept": "Account"}
{ "create" : { "_index": "employee0209" } }
{ "sentinel_one.agent.uuid": "72e6408d1fb840a89dd9596aa03b4825", "ip": "172.16.4.128", "mac": "00-0C-29-0E-F9-D6", "username": "user4", "dept": "Marketing"}
1. enrich 정책 생성
PUT _enrich/policy/employee-policy1
{
"match": {
"indices": "employee0209",
"match_field": "sentinel_one.agent.uuid",
"enrich_fields": ["ip", "mac", "username", "dept"]
}
}
2. enrich 정책 실행
POST /_enrich/policy/employee-policy1/_execute
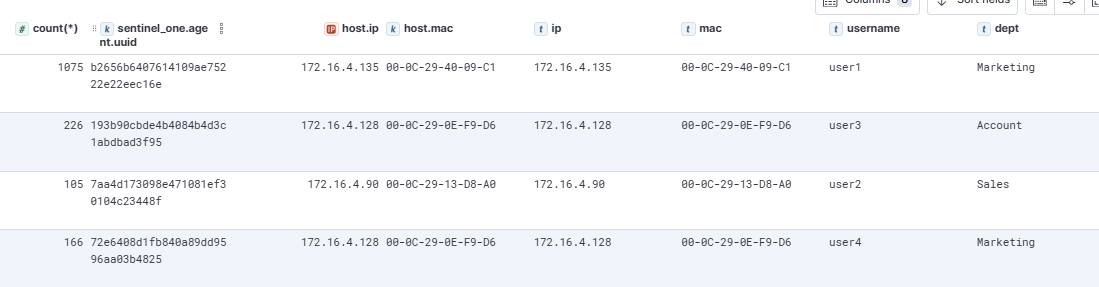
FROM logs-sentinel_one.agent-kdb
| where sentinel_one.agent.uuid IS NOT NULL
| ENRICH employee-policy1 on sentinel_one.agent.uuid
| STATS count(*) by sentinel_one.agent.uuid, host.ip, host.mac, ip, mac, username, dept
first\last
FROM logs-sentinel_one.agent-default
| where sentinel_one.agent.uuid IS NOT NULL
| SORT @timestamp DESC
| STATS ip=TOP(sentinel_one.agent.uuid, 1, "desc") by sentinel_one.agent.network_interfaces.inet'제품 > ELK' 카테고리의 다른 글
| 데이터 가져오기 (0) | 2025.02.15 |
|---|---|
| 로그스태시로 데이터베이스에서 레코드 가져오기 (0) | 2025.02.13 |
| 로그스태시 - RDBMS 데이터를 Elasticsearch에 넣기 (0) | 2025.01.27 |
| Logstash에서 민감한 설정 보호하기: Keystore사용법 (0) | 2025.01.19 |
| 타임스탬프 (0) | 2024.10.15 |


